MetaSploit tutorial for beginners
This MetaSploit tutorial for beginners is meant to be a starting guide on how to use MetaSploit if you have never used it before. It assumes that you already have MetaSploit installed and that it works, or that you are running Kali / other pen testing distro of linux (eg Parrot or BlackArch).
Metasploit history
Metasploit was created by H. D. Moore in 2003 as a portable network tool using Perl.
Metasploit 3.0 began to include fuzzing tools, used to discover software vulnerabilities, rather than just exploits for known bugs. This avenue can be seen with the integration of the lorcon wireless (802.11) toolset into Metasploit 3.0 in November 2006.
By 2007, the Metasploit Framework had been completely rewritten in ruby.
On October 21, 2009, the Metasploit Project announced that it had been acquired by Rapid7, a security company that provides unified vulnerability management solutions.
Metasploit 4.0 was released in August 2011
Metasploit Framework is opensource and you can view their code repo here: https://github.com/rapid7/metasploit-framework
Using Metasploit
The basic concept you need to use in order to know how to use MetaSploit is pretty easy when you have used the tool a few times and is as follows:
– Run msfconsole in your terminal
– Identify a remote host and add to the metasploit database
– Identify a vulnerability in the remote host that you wish to exploit
– Configure the payload to exploit the vulnerability in the remote host
– Execute the payload against the remote host
Once you have practiced and mastered this pattern, you can perform most of the tasks within Metasploit. As this is a MetaSploit tutorial for beginners, I’ll walk you through the steps you need to know to scan your first machine.
If you enjoy this tutorial, please check out my metasploit tutorials below
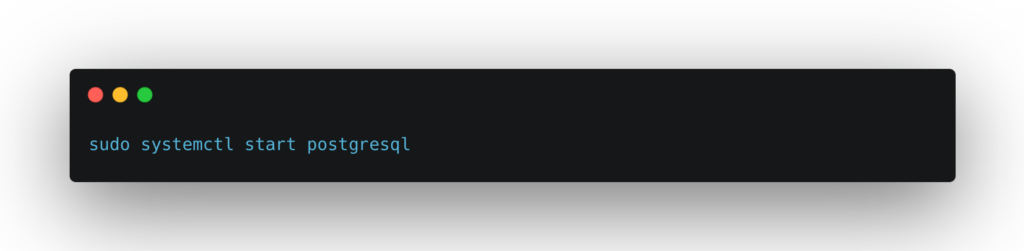
Start the database service
In your favourite Kali Linux Terminal (I recommend terminator), run the following command to start up a database server on your machine. This database is used to store all your results (so that you can come back to them later on, or share the database with others if working on a team)
If this is the first time you are running metasploit, then you will need to run the following command to create a database schema

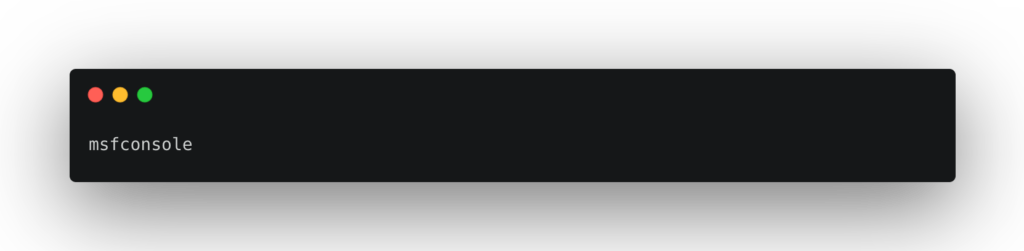
You can now start metasploit using the msfconsole command from the terminal
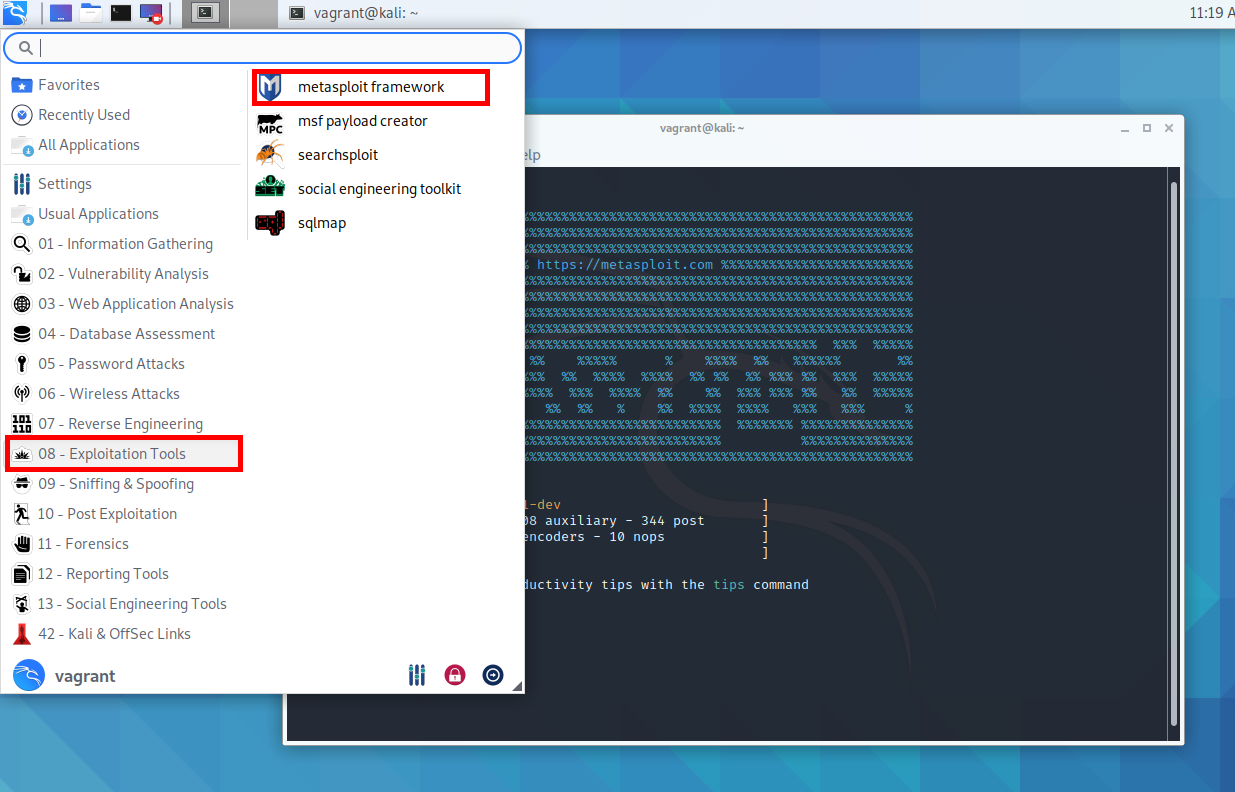
Or using the kali linux menu system you will find it under “Exploitation tools > metasploit framework”
Once Metasploit has loaded you will meet with the following prompt in your terminal – the splash screens are random, so don’t worry if yours looks different:
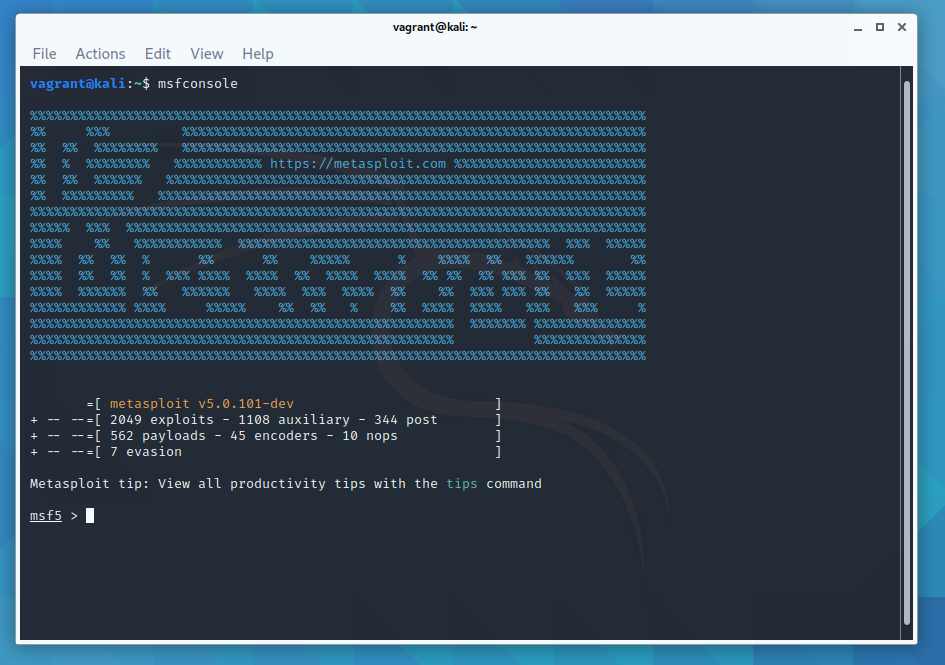
This is msfconsole. Msfconsole is the main command line interface to MetaSploit. There are other interfaces available – GUI interfaces (armitage), and a web interface too (websploit). With msfconsole you can launch exploits, create listeners, configure payloads etc.
Getting help in metasploit
MetaSploit has lots of great documentation built in. You can access this documentation if you type help to get a basic list of commands.

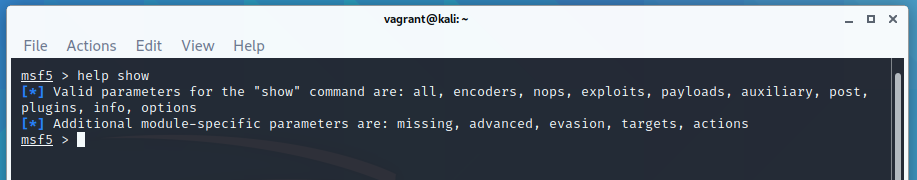
help show will give you the help section for the show command. You can then pass additional queries, such as show exploits

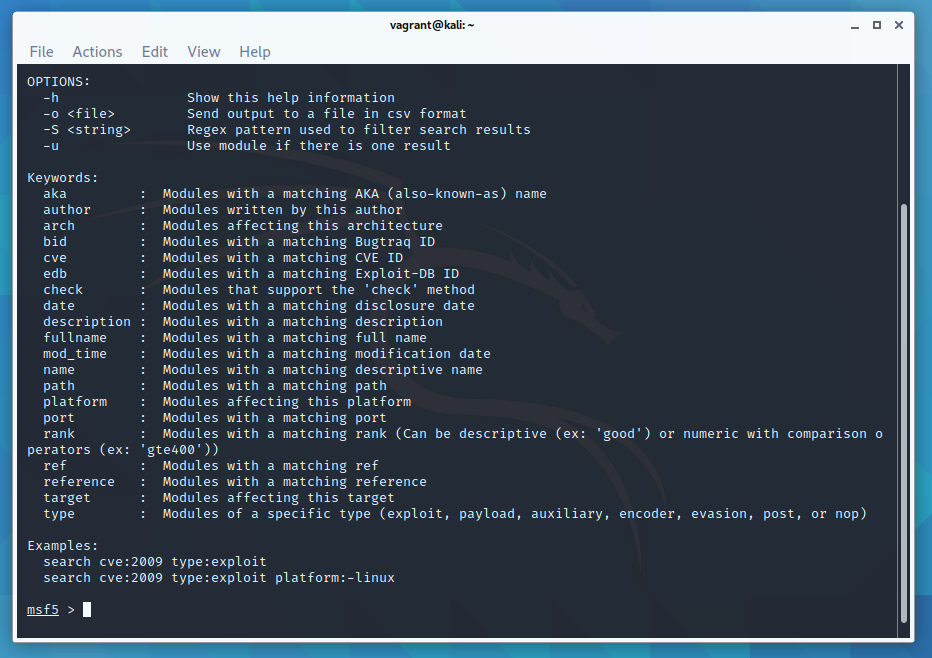
help search will give you the help section for the search command
To show a list of all available port scanners:

More examples of port-scanning remote machines and saving the output into the metasploit database are here
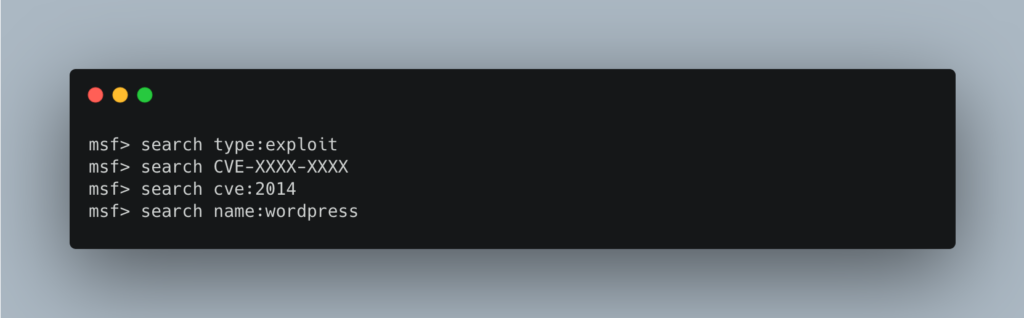
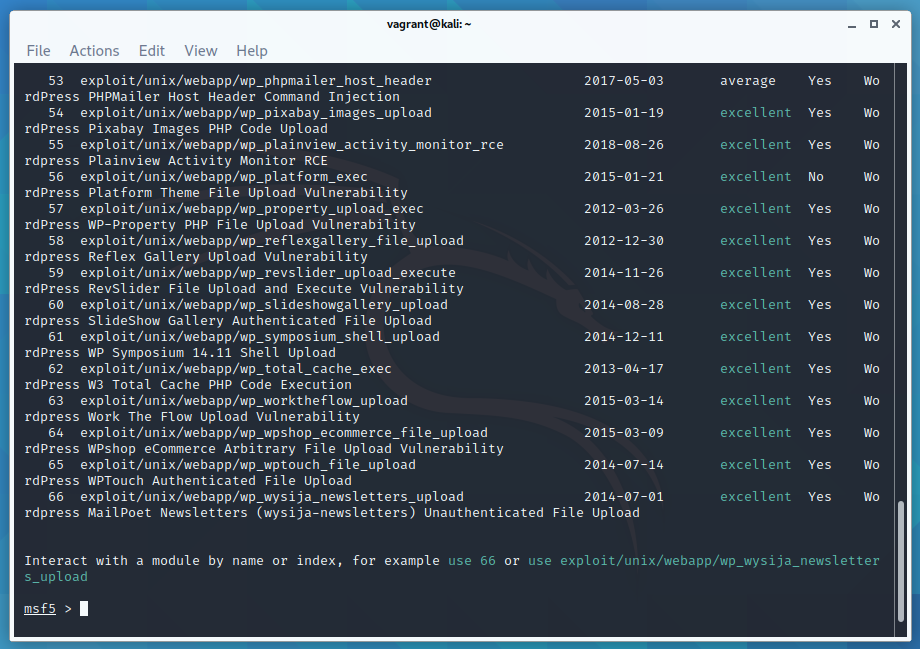
There is also a way to search within msfconsole for various exploits:
See metasploit unleashed for more examples of the search command
Identify a remote host – run an nmap scan inside metasploit
You can now run an nmap scan from inside msfconsole and save the output into the MetaSploit database.
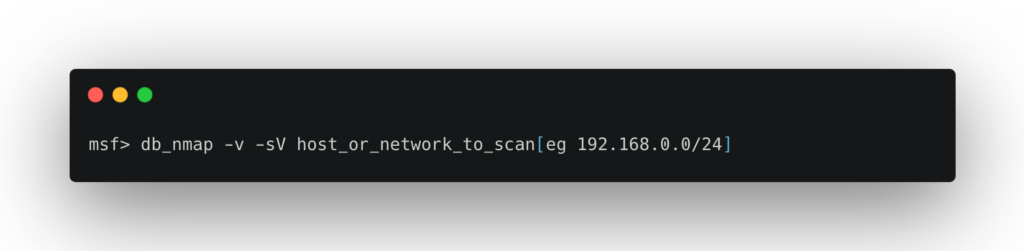
This is a handy way to get an initial list of remote hosts on your network. I have some other tips in this linux commands for networking article.
To list all the remote hosts found by your nmap scan:

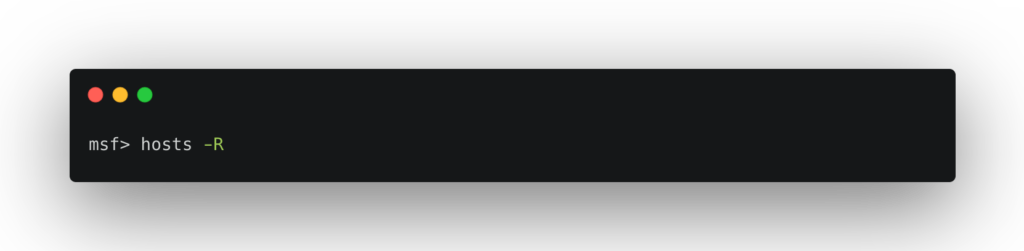
To add these hosts to your list of remote targets
MetaSploit tutorial for beginners – Pick a vulnerability and use an exploit
Once you have performed an operating system fingerprint (or you have identified the application running on the remote host, eg by imporing nessus results into metasploit) and know what your remote hosts operating system is (using nmap, lynix, maltego, wp-scan, etc) you can pick an exploit to test. rapid7 have an easy way to find exploits. There is also a way to search within msfconsole for various exploits:
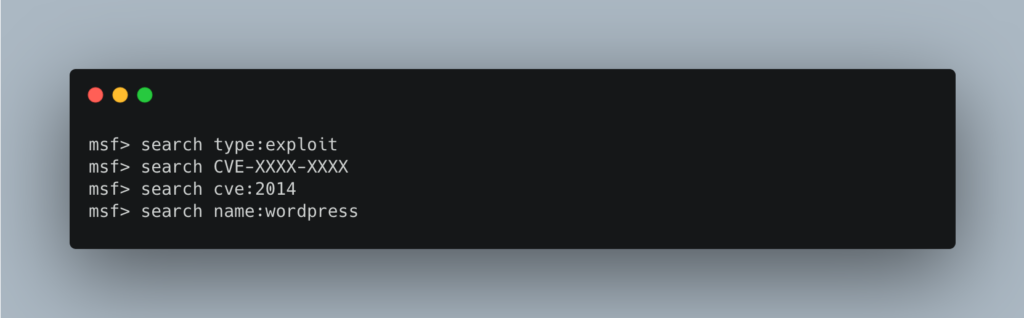
See metasploit unleashed for more examples of the search command
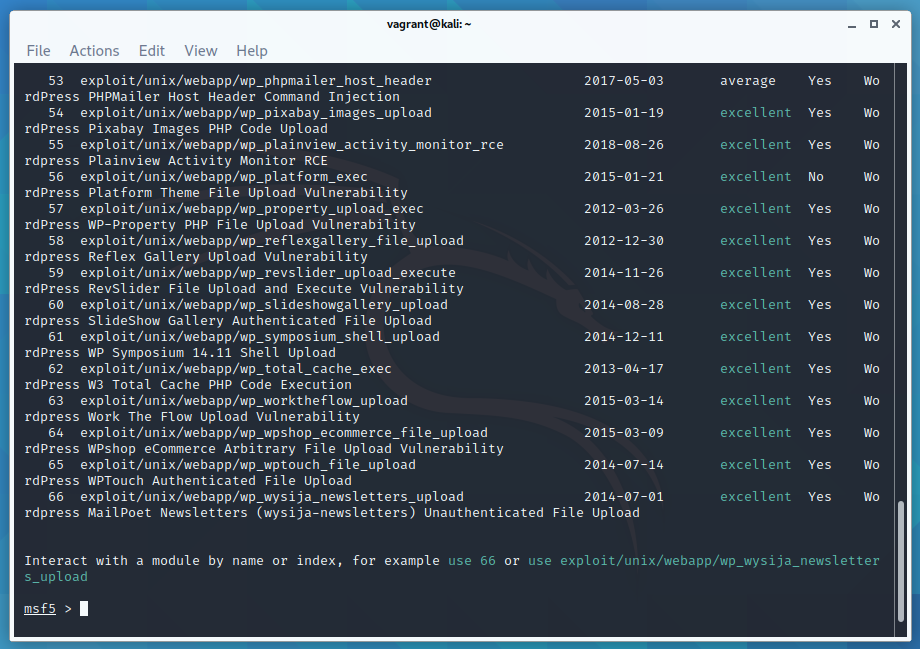
Once you have found a suitable exploit to use against the vulnerability in the remote host, issue the following command into msfconsole:
eg: use exploit/unix/webapp/php_wordpress_total_cache
From this point on, the available options change based on the exploit you are using, but you can get a list of the available options with:

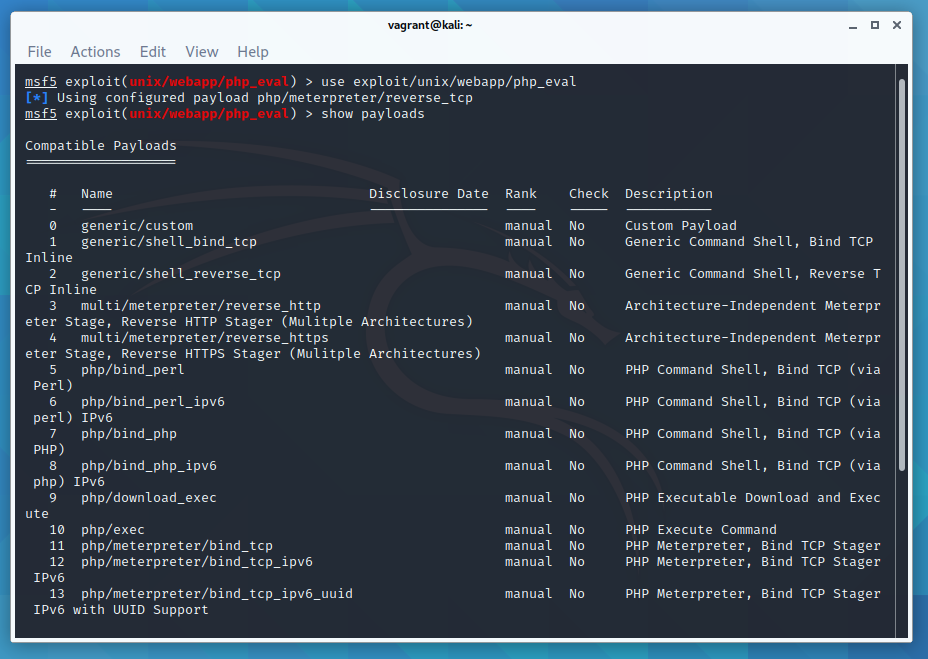
For a list of the available targets:

MetaSploit tutorial for beginners – Configure the exploit
In MetaSploit each exploit has a set of options to configure for your remote host:

This gives a list. You need to set the options with ‘yes’ next to them in the ‘required’ column.
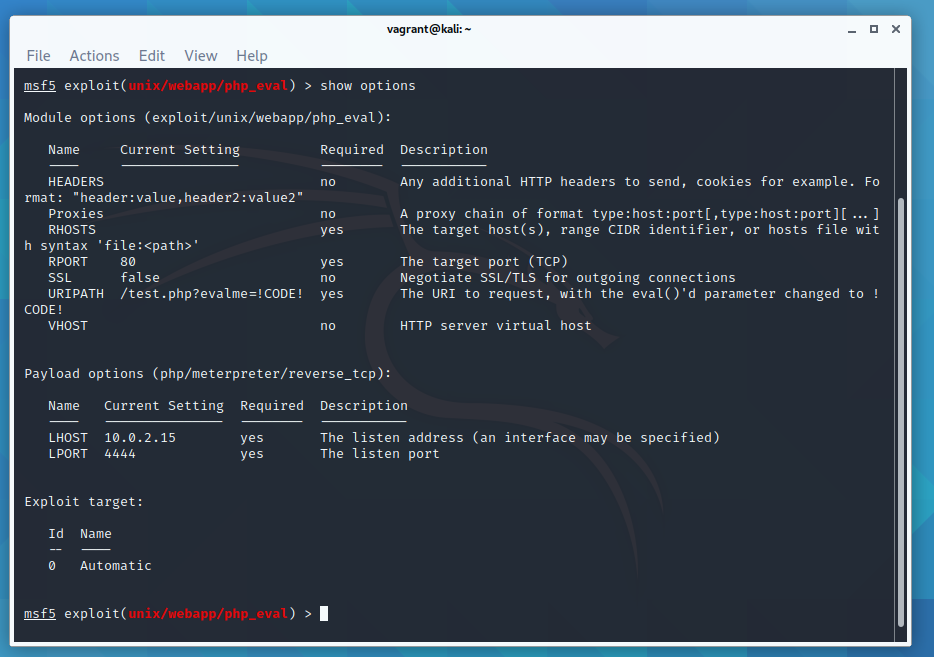
If you issue the ‘hosts -R’ command then you will see that the remote hosts parameters are already filled in for you.
Execute the exploit against the remote host

or

If metasploit is successful in exploiting the vulnerability, you will know – most likely it will pop a shell for you. If you don’t get a shell, then your exploit may not have worked – you may have to try a different exploit for the same vulnerability, or you may have to gain better information on your targets – perhaps you wrongly identified the version of the service.
Thats the very basics of using metasploit covered! I hope you enjoyed my basic metasploit tutorial for beginners.
If you enjoy this tutorial, please check out my metasploit tutorials below
References which I used to make this guide:
Kali Metasploit Guide
offensive security – metasploit unleashed – using exploits
offensive security – metasploit unleashed – msfconsole commands

what if no hosts are detected???
Then nobody to run anything against to.
hey i am using kali 2.0 , I would like to use msf over wan or public domain . will you please suggest or make good article on it . thanks in advance
ok thank you so much for the help i just have one question how do i find the rports
how do i know which exploit to grab?
typo on database start command, should be
service postgresql start
thanks :)
fixed now
no, it’s not
I had restored a previous revision and it reinstated the typo :)
It should be good for now
for how to install metasploit in the windows check here how to install metasploit on windows OS for how to install metasploit in the windows check here https://www.fhxploit.com/2018/05/cara-memasang-metasploitframework-di.html