Continuing on from my original metasploit beginners tutorial, here is a slightly more advanced Metasploit tutorial on how to use metasploit to scan for vulnerabilities. The outcome of this tutorial will be to gather information on a host and its running services and their versions and vulnerabilities, rather than to exploit an unpatched service.
If you enjoy this tutorial, please check out my metasploit tutorials below
The first point in how to use metasploit to scan for vulnerabilities is that you should only do this against websites, servers or web apps that you own, or have permission to do this against!
For this how to use metasploit to scan for vulnerabilities tutorial I am going to walk through some simple website hacking techniques using metasploit – these will be useful if you are a blue team member to help secure your site, and if you are a beginner red team member to polish your skills. I have a list of references used at the end for further reading.
How to use metasploit to scan for vulnerabilities – Tools needed
1) dvwa on vagrant
2) metasploit (I recommend kali linux on a laptop or tablet)
3) ???
4) 1337 skillz
Firstly, we want to fire up our dvwa vagrant box from my tutorial.
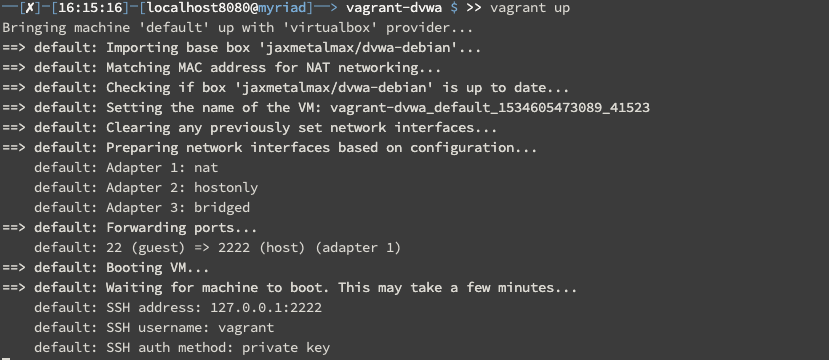
Once our DVWA is up and running (following the link to my tutoral – we need two adaptors for our virtualbox), we can save ourselves a ton of time by ssh’ing into the vagrant box and getting its IP address. See this post about how to scan networks for IP addresses and intreresting ports if you want / need practice in that area.
vagrant ssh ip-addr
In my case, the ip address for my dvwa vagrant box is 192.168.0.120, I’ll be using this throughout the tutorial, please change as needed
Information gathered:
- Target Hosts IP address
As always, I start with a regular ping to see if the host is reachable
ping 192.168.0.120
How to use metasploit to scan for vulnerabilities – Starting Metasploit
Once we have established a route to the host (if ping returns us a result) then fire up postgresql and msfconsole
service postgreqsql start
if this is the first time you are running metasploit, run the following:
msfdb init
start metasploit using msfconsole
msfconsole
How to use metasploit to scan for vulnerabilities – Scanning a host
Once msfconsole is running, we can run an nmap scan of the target host from inside msfconsole, adding results to our database for later exploration:
db_nmap -v -sV 192.168.0.120
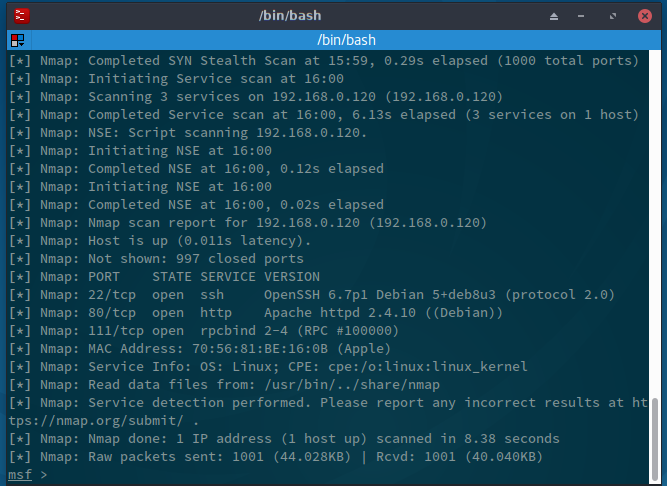
From the results, we can see port 22 is open, port 80 is open and port 111 is open. As a side note, we can see the mac address of this host, and its OS fingerprint too. These can come in useful later on.
Information gathered:
- Hosts IP address
- Running services (ssh, http, rpc)
- our httpd doesnt run in ssl mode (https)
I usually perform a second nmap scan here, with some more detailed info on the ports (and it has a nicer output because it doesnt have the -v flag)
db_nmap -sS -Pn -A 192.168.0.120
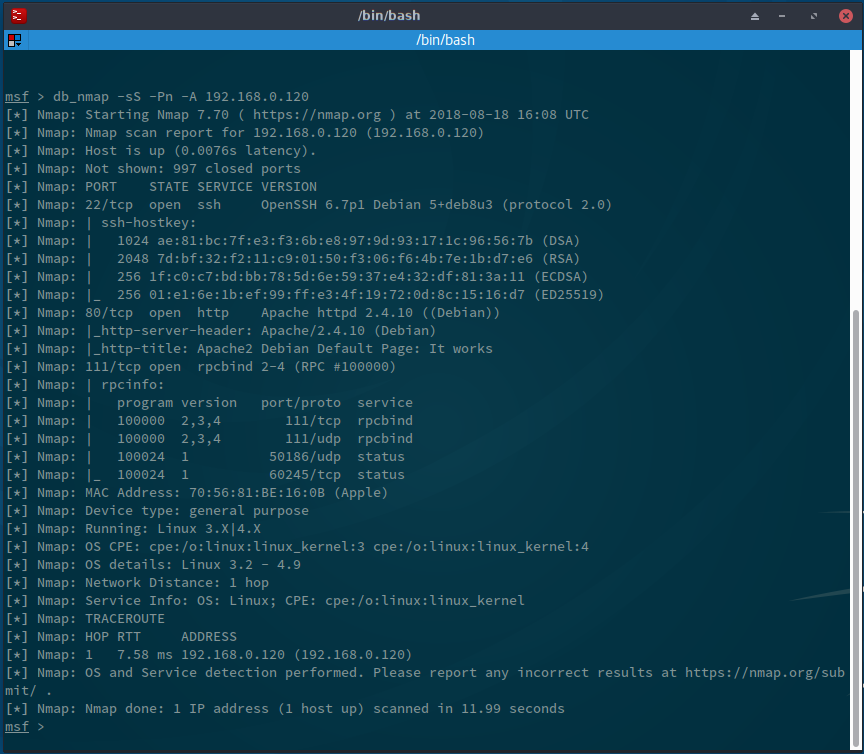
Information gathered:
- Hosts IP address (192.168.0.120)
- Running services (ssh, http, rpc)
- our httpd doesnt run in ssl mode (https)
- O/S – Debian (or debian derivative)
- O/S version (Linux 3.2 – 4.9)
- Service Versions (apache 2.4.10, rpcbind 2.4, openssh 6.7p1)
- host ssh fingerprints
- host supported cypher protocols (DSA, RSA, ECDSA, ED25519)
- number of hops to host (1)
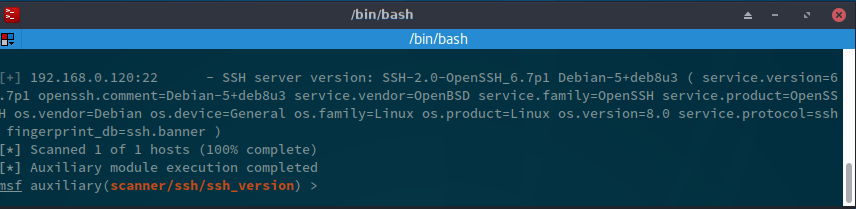
Next is to check our sshd service version:
use scanner/ssh/ssh_version set RHOSTS 192.168.0.120 set THREADS 50 run
We had the information previously, but its always nice to verify before continuing.
How to use metasploit to scan for vulnerabilities – finding an exploit
I’ll have a check in metasploits database for vulnerabilities now, to see if there is any low hanging fruit (I dont like to jump right in with a full blown nessus scan, after all we are trying to hone our abilities, not sledgehammer our own machine!)
search name:httpd
There are a few exploits listed, but the internet is better: https://www.rapid7.com/db/search is rapid7’s vulnerability database. plugging in services and versions (eg search for apache 2.4.10) and you can see vulnerabilities. You can also change the search parmeter to search the metasploit modules (this is the same as searching inside metasploit). https://www.cvedetails.com is one that I personally like as it categories CVE’s by application and version.
Rinse and repeat for each of our identified resources.
Information gathered:
- Hosts IP address (192.168.0.120)
- Running services (ssh, http, rpc)
- our httpd doesnt run in ssl mode (https)
- O/S – Debian (or debian derivative)
- O/S version (Linux 3.2 – 4.9)
- Service Versions (apache 2.4.10, rpcbind (0.)2.4, openssh 6.7p1)
- host ssh fingerprints
- host supported cypher protocols (DSA, RSA, ECDSA, ED25519)
- number of hops to host (1)
- known vulnerabilities for apache 2.4.10
- known vulnerabilities for sshd 6.7p1
- known vulnerabilities for rcpbind
How to use metasploit to scan for vulnerabilities
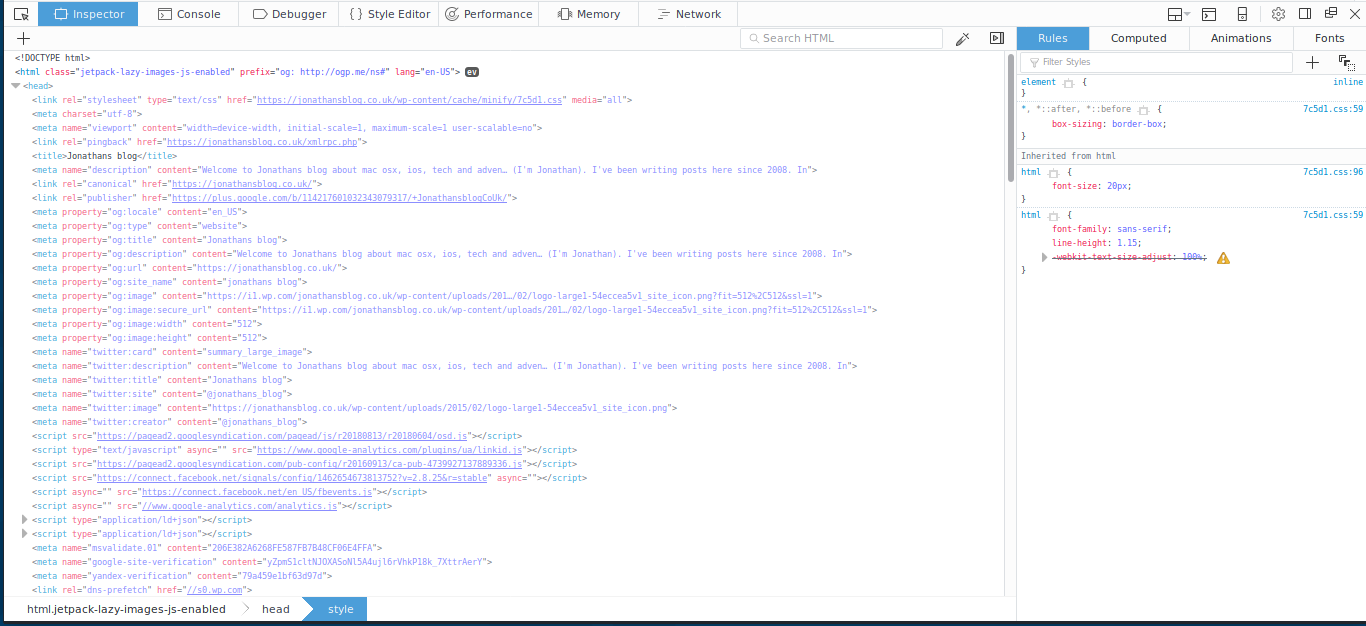
A useful thing here is the firefox developer tools (right click > inspect element) – they can give you full header information, and you can view source-code. There are a few other tools in your arsenal that you can use to identify popular website platforms:
Does the server run wordpress?
Easiest way to tell if the site is running wordpress is to visit the site in your browser and view source, you’ll see /wp-content/ everywhere *(unless the admins have changed the structure of wordpress)
Tools for gathering information about wordpress
plecost
wpscan
if you are looking at a wordpress, then you can use wpscan to list all the versions of the installed themes and plugins. you can then use cvedtails and the rapid7 db search to find vulnerabilities and exploits.
does the server run magento / drupal / joomla / something else?
does the server run php / python / nodejs?
does the server run apache or nginx or iis?
hint: if you are looking at wordpres, you are also running php and mysql (possibly apache and/or nginx too). Take time to get familiar with the frameworks and technology stacks – there are lots (ruby on rails, django, nodejs, vue, react, laravel, php, wordpress, drupal, joomla, .net, elk stack, the list goes on and on)
An easy way to tell this is with the firefox developer tools *(or a curl command, or from the nmap portscan in metasploit earlier)
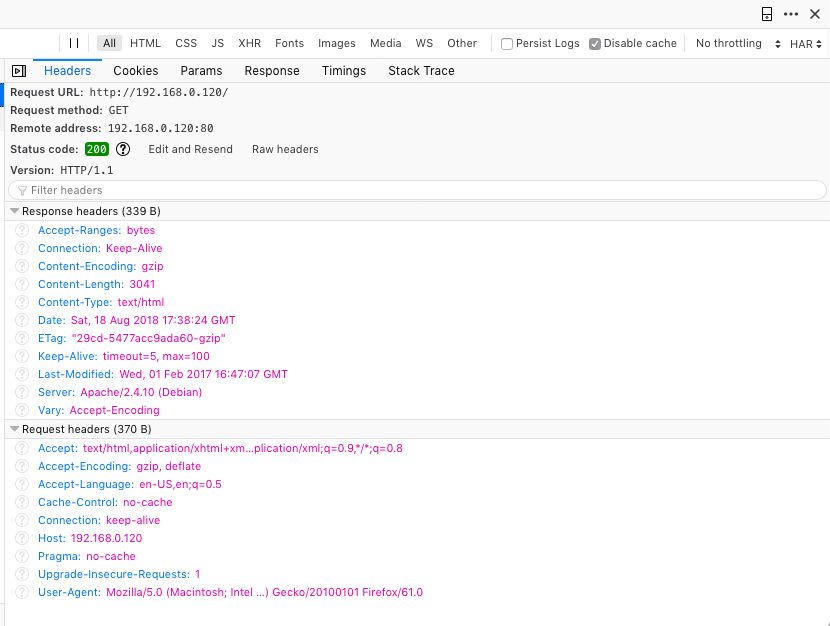
to get the headers in firefox, right click > inspect > network > click on the request you want to view > click on headers
if you are looking at a nginx / drupal / django, or any other web stack / technology you can then use cvedtails and the rapid7 db search to find vulnerabilities and exploits.
are we on a cloud, eg aws, azure?
again, firefox developer tools, traceroutes, etc
what about web application firewalls (cloudflare, etc)?
again, firefox developer tools, traceroutes, dns lookups
Information gathered:
- Hosts IP address (192.168.0.120)
- Running services (ssh, http, rpc)
- our httpd doesnt run in ssl mode (https)
- O/S – Debian (or debian derivative)
- O/S version (Linux 3.2 – 4.9)
- Service Versions (apache 2.4.10, rpcbind (0.)2.4, openssh 6.7p1)
- host ssh fingerprints
- host supported cypher protocols (DSA, RSA, ECDSA, ED25519)
- number of hops to host (1)
- known vulnerabilities for apache 2.4.10
- known vulnerabilities for sshd 6.7p1
- known vulnerabilities for rcpbind
- platforms and stacks the remote webservice is running
- Versions of those stacks and apps and plugins and themes
- known vulnerabilities of those stacks and apps and plugins and themes
The last stage in how to use metasploit to scan for vulnerabilities process is to search for exploits for the known vulnerabilities (or, even better, to make your own) – I wont be covering this yet, but there are plenty of resources online, and my beginners tutorial may help.
If you enjoy this tutorial, please check out my metasploit tutorials below
How to use metasploit to scan for vulnerabilities References:
Matasploit – the penetration testers guide ISBN:978-1-59327-288-3
https://cvedetails.com
https://www.offensive-security.com/metasploit-unleashed/msfconsole-commands/
https://rapid7.com/db/search

Leave a Reply
You must be logged in to post a comment.