This post is a wapiti tutorial. You’ll find various wapiti options, how to import wapiti scan results into metasploit and how you can disable wapiti modules to speed up your scans.
Wapiti is an open-source web application vulnerability scanner designed to identify security weaknesses in web applications. It operates by performing a thorough assessment of a web application’s structure and detecting potential vulnerabilities like SQL injection, cross-site scripting (XSS), and file inclusion flaws.
Wapiti Features:
- Active and Passive Scanning: Wapiti employs both active and passive scanning methods. Active scanning involves sending specially crafted requests to the web application to probe for vulnerabilities, while passive scanning analyzes the responses to identify weaknesses.
- Comprehensive Reporting: After completing a scan, Wapiti generates detailed reports highlighting identified vulnerabilities along with potential risk levels. This information is essential for developers and security teams to prioritize remediation efforts.
- User-Friendly Interface: Wapiti provides a command-line interface that makes it accessible for users with varying levels of technical expertise. It also supports various output formats, including HTML, XML, and TXT, which facilitates easy integration into existing security workflows.
- Customizable: Users can tailor the scanning process by configuring various parameters, such as specifying URLs, adjusting timeout settings, or selecting specific modules to scan for particular vulnerabilities. This flexibility allows users to focus on their application’s unique security needs.
A basic one-liner command to get you started would be:
wapiti https://example.org/cool-things -u -n 5 -b domain -v 2 -o /tmp/outfile.html
More about the command line arguments:
-u, --color
use colours
-b, --scope
set the scope of the scan:
page: only analyse the page given in the url
folder: analyse all urls in the root url given (default option)
domain: analyse all links to pages in the same domain
-n, --nice
use this to prevent infinite loops, I usually go with 5
-f,
--format
change the output format
json:
html:
openvas:
txt:
vulneranet:
xml:
-v verbose
0: none
1: print each url
2: print each attack
# if you don't specify a -v flag, then you get a blank screen for ages
These basics will help you build the first command above, and will show you what the options mean.
There is a man page for wapiti, which has lots of information in it, including how to exclude patterns (useful once you know more about a host and want to narrow in on a target)
the openvas format is good too, as it allows you to import into openvas.
It will take a while to run a full scan on your target if you include all of the modules
Wapiti tutorial: Disabling specific scan modules
wapiti comes with built in modules to test for various vulnerabilities in your remote targets:
backup: This module search backup of scripts on the server.
blindsql: Time-based blind sql scanner.
crlf: Search for CR/LF injection in HTTP headers.
exec: Module used to detect command execution vulnerabilities.
file: Search for include()/fread() and other file handling vulns.
htaccess: Try to bypass weak htaccess configurations.
nikto: Use a Nikto database to search for potentially dangerous files.
permanentxss: Look for permanent XSS.
sql: Standard error-based SQL injection scanner.
xss: Module for XSS detection.
buster: Module for a file and directory buster attack – checking for “bad” files.
shellshock: Module for Shellshock bug detection.
you can exclude modules with the -m flag, and you can exclude all modules with -m “-all”
to scan only for sql and blindsql attacks, you can use the following parameters:
-m "-all,sql,blindsql"
# eg
wapiti https://example.org/cool-things -u -n 5 -b domain -m "-all,sql,blindsql" -v 2 -o /tmp/outfile.html
this will disable all modules, then re-enable the blindsql module
Wapiti tutorial: Wapiti output
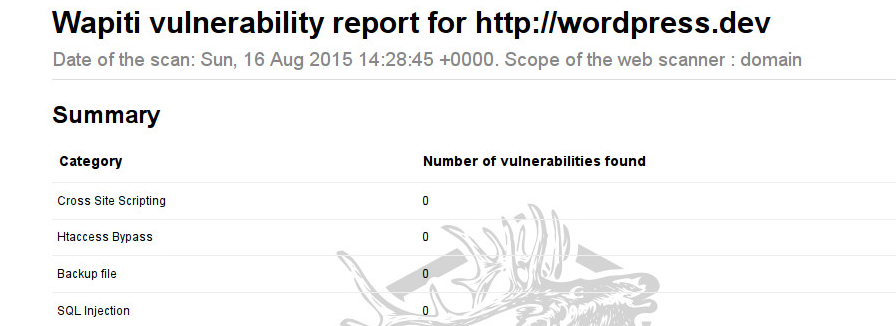
Watapi generates various types of output, I usually go for html first, and then xml to import into metasploit
-f, --format
change the output format
json:
html:
openvas:
txt:
vulneranet:
xml:
Wapiti in metsploit
You can import wapiti scans into metasploit, and have the results added to your metasploit database.
fire up msfconsole
msfconsole
# type
db_import
you will see the available importers, wapiti is the last one
to import a wapiti scan, the result has to be saved as an xml file
you use the -f xml flag for wapiti to output an xml file do this
To import the wapiti xml file into metasploit, run the following from insode msfconsole
db_import /tmp/outfile.xml
The results will be imported into the metasploit database
Cookies, csrf tokens and other things
Most web applications use csrf tokens and cookies. To do anything thats locked behind an authentication (eg behing the login area) you can pass credentials to wapiti
you can also pass an authenticated cookie to wapiti so that it can pages that require authentication.
look at the -c, –cookie section in the man page
Sources:
https://www.owasp.org/index.php/Automated_Audit_using_WAPITI
https://www.owasp.org/index.php/Automated_Audit_using_WAPITI
Leave a Reply
You must be logged in to post a comment.