Nick Dorling, Systems Engineering Manager at Palo Alto

A lot if the solutions rely on installing an agent on a device. It means that they get good insight to that device, but not to devices that cant run their agent…
That said, the palo alto systems seem really good, if you are all cloud based and want that fine grained zero trust setup the best thing I think though is the redundancy from their peering with the big cloud providers all over the globe
Zero Trust and Palo Alto Prisma: Redefining Modern Network Security
Zero Trust is a security philosophy built on a simple but powerful premise: trust nothing, verify everything. Unlike traditional perimeter-based security models — where anyone inside the network was implicitly trusted — Zero Trust assumes that threats can exist both outside and inside the organisation. Every user, device, and application must be continuously verified before being granted access, regardless of their location.
This shift matters because the modern enterprise has fundamentally changed. Workforces are hybrid, applications live in the cloud, and the old idea of a defined network perimeter has largely dissolved. In this environment, a “castle and moat” approach leaves organisations dangerously exposed.
Palo Alto Networks and the Prisma Platform
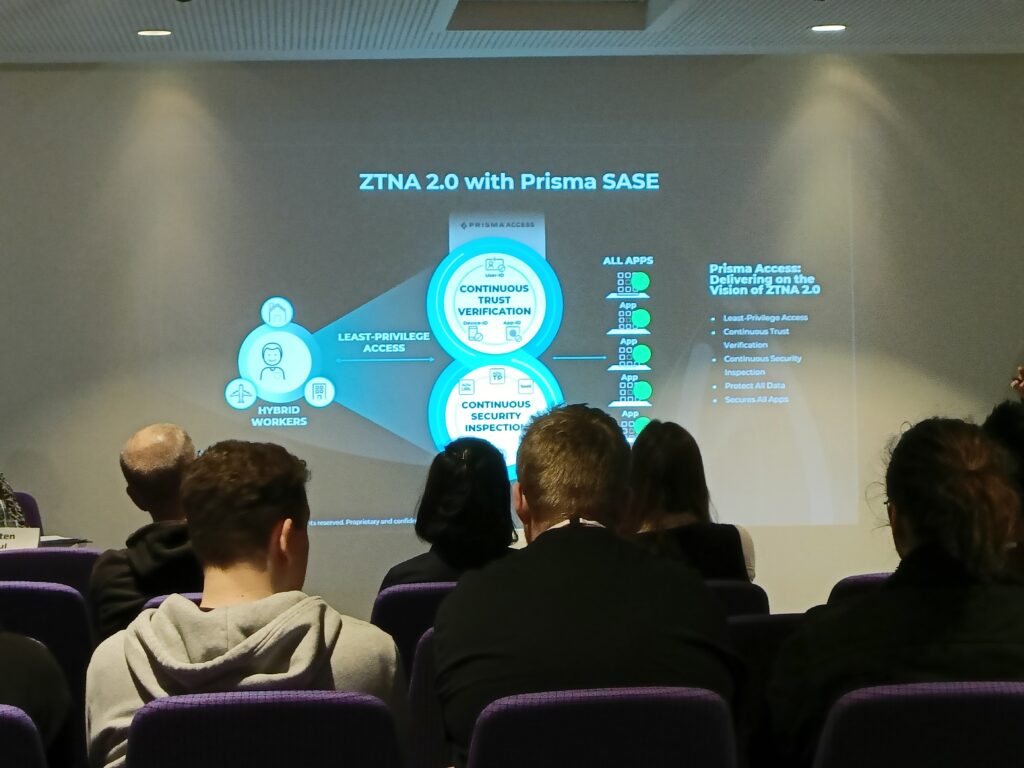
Palo Alto Networks has positioned itself as a cornerstone of enterprise Zero Trust through its Prisma portfolio, which sits at the heart of its Secure Access Service Edge (SASE) architecture. Prisma Access serves as the core of Palo Alto Networks’ SASE architecture, unifying network and security functionalities under one scalable, cloud-delivered platform.
The evolution of their Zero Trust approach is best understood through the lens of ZTNA — Zero Trust Network Access. Palo Alto Networks argues that first-generation ZTNA solutions fell short in a critical way: once access was granted, that connection was implicitly trusted forever. With ZTNA 1.0, once access to an app is granted, that communication is implicitly trusted forever, regardless of user or app behaviour changes, or if malicious activity takes place. Their response was ZTNA 2.0, embedded within Prisma Access.
What ZTNA 2.0 Brings to Zero Trust
ZTNA 2.0 combines fine-grained, least-privileged access with continuous trust verification and deep, ongoing security inspection to protect all users, devices, apps, and data everywhere — all from a single unified product. This means the platform doesn’t simply open a door and walk away. It watches continuously, ready to revoke access the moment something looks wrong.
A key part of this is moving away from coarse, network-level controls. ZTNA 1.0 solutions leverage coarse-grained controls based on low-level networking constructs like IP address and port number — an approach that provides too much access and leaves organisations exposed to increased risk. Prisma replaces this with identity-based, application-aware controls that operate at a much more granular level.
Continuous Verification in Practice
The platform enforces identity-based access control at every network layer, ensuring least-privilege connectivity for both on-premises and remote users. This is complemented by tighter integrations with identity providers such as Okta and Microsoft Entra ID, giving security teams centralised visibility and governance across their entire user base.
Palo Alto Networks’ comprehensive Zero Trust platform is designed to minimise the attack surface, prevent unauthorised access, and limit the lateral movement of threats — ensuring that only validated and authorised activity occurs across the network, applications, and data.
Industry Recognition
The strategy appears to be resonating. Palo Alto Networks was named a Leader in The Forrester Wave: Zero Trust Platforms, Q3 2025, achieving the highest score in the Current Offering category.
In short, Palo Alto Prisma translates Zero Trust from a philosophy into an operational framework — one where access is earned continuously, not granted once and forgotten.

Leave a Reply
You must be logged in to post a comment.