My research notes about the different types of sqli – sql injection attack types;
inband (eg reading errors from the screen)
out-of-band (getting information from a different channel eg from an email after the attack)
inferrential (or blind) – getting an error from a system that allows you to re-construct the internals / queries
tautologies: – injecting code into a conditional statement so that it always evaluates as true
Illegal / locally incorrect queries: – essentially generating an error in the database
Union queries – essentally adding ‘UNION SELECT <query>’ to the end of existing queries
Piggy Back queries – essentially adding a delimiter (;) and a second query to existing queries
Stored procedures – executing / injecting / modifying stored procedures
Inference – inferring information, eg exploitable parameters, when no usable error reporting is viewable
Alternate encodings – using alternative character encoding to generate errors
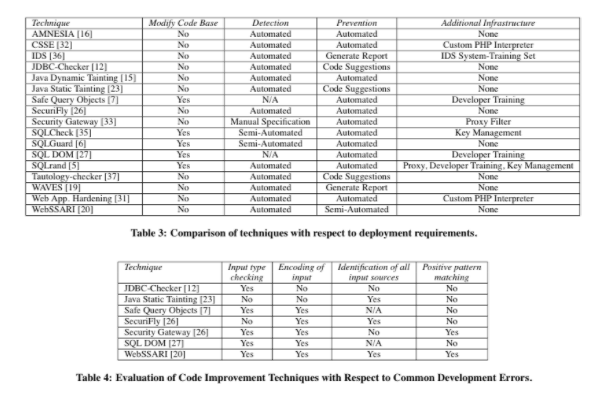
Paper: A Classification of SQL Injection Attacks and Countermeasures – halfond 2006
There is an excellent section on detection methodologies:
- – black box testing
- – Static code chekers
- – combined static and dynamic analysis
- – new query development paradigms
- – intrusion detection
- – proxy filters
- – instruction set randomisation
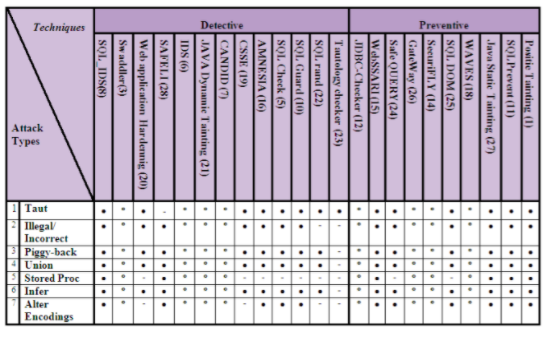
And an evaluation of tools from each of the methodologies and how they perform for each of the types of sqli – sql injection attack types.
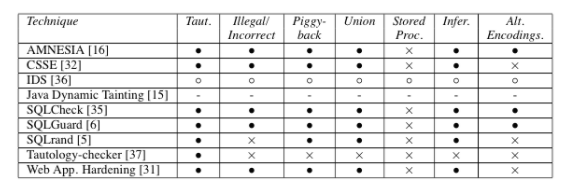
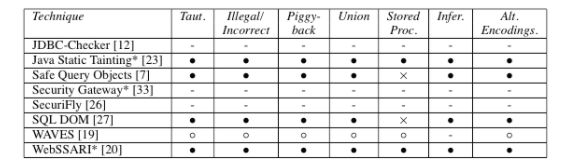
And a very handy table to summarise the implementations of the tools
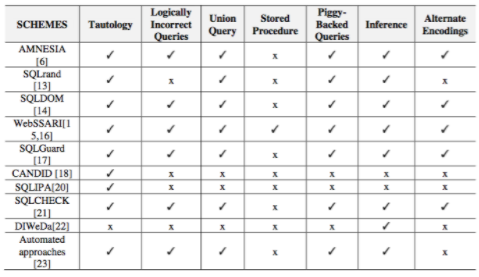
paper: SQL Injection Detection and Prevention Techniques
International Journal of Advancements in Computing Technology Volume 3, Number 7, August 2011
Atefeh Tajpour, Suhaimi Ibrahim, Maslin Masrom
3. CLASSIFICATION OF SQLIA
Depending on many factors, SQL Injection attacks can be divided into several groups. Here, there are two categories in which are possible to unite all the SQLIAs. This classification is according to the main publications related to the phenomena of SQL Injection [2].
3.1. By Intent
An important classification of SQLIA is related to the attacker’s intent, or in other words, the goal of the attack [4].
- Extracting data – This category of attacks tries to extract data values from the back end database. Based on the type of web application, this information could be sensitive, for example, credit card numbers, social numbers, private data are highly valuable to the attacker. This kind of intent is the most common type of SQLIA.
Adding or modifying data – The purpose of these attacks is to add or change data values within a database.
Performing database finger printing– In this category of attack the malicious user wants to discover technical information on the database such as the type and version that a specific web application is using. It is noticeable that certain types of databases respond differently to different queries and attacks, and this information can be used to “fingerprint” the database. Once the intruder knows the type and the version of the database it is possible to organize a particular attack to that database.
- Bypassing authentication-By this attack, intruders try to bypass database and application authentication mechanisms. Once it has been over passed, such mechanisms could allow the intruder to assume the rights and privileges associated with another application user.
- Identifying injectable parameters– Its goal is to explore a web application to discover which parameters and user-input fields are vulnerable to SQLIA. By using an automated tool called a “vulnerabilities scanner” this intent can be identified.
- Determining database schema-The goal of this attack is to obtain all the database schema information (such as table names, column names, and column data types). This is very useful to an attacker to gather this information to extract data from the database successfully. Usually by exploiting specific tools such as penetration testers and vulnerabilities scanners this goal is achieved.
- Evading detection– in this category attackers try to avoid auditing and detection, including evading defensive coding practices and also many automated prevention techniques. These attack techniques try to bypass Intrusion Detection and Prevention or other security mechanisms which provide security for systems.
- Performing denial of service– in this category intruders make interrupt in system services by performing some instruction so the database of a web application shutdown, thus denying service happen. Attacks involving locking or dropping database tables also fall into this category.
- Executing remote commands-The goal of this action is to execute arbitrary commands on the database. These commands can be stored procedures or functions available to database users. This kind of attack is the most dangerous because it may allow the intruder to gain control of the whole system. For instance Microsoft’s SQL Server supports a stored procedure xp – cmdshell that permits to arbitrary command execution, and if this attack runs then complete compromise of the server is unavoidable.
3.2. By Type
There are different methods of attacks. Depending on the goal of attacker are performed together or sequentially. For a successful SQLIA the attacker should append a syntactically correct command to the original SQL query. Now the following classification of SQLIAs in accordance to the Halfond, Viegas, and Orso researches [4, 11] will be presented.
- Tautologies: This type of attack injects SQL tokens to the conditional query statement to be evaluated always true.
- Illegal/Logically Incorrect Queries: when a query is rejected, an error message is returned from the database including useful debugging information. This error messages help attacker to find vulnerable parameters in the application and consequently database of the application.
- Union Query: By this technique, attackers join injected query to the safe query by the word UNION and then can get data about other tables from the application.
- Piggy-backed Queries: In this type of attack, intruders exploit database by the query delimiter, such as “;”, to append extra query to the original query. With a successful attack database receives and execute a multiple distinct queries. Normally the first query is legitimate query, whereas following queries could be illegitimate.
- Stored Procedure: Stored procedure is a part of database that programmer could set an extra abstraction layer on the database. As stored procedure could be coded by programmer, so, this part is as inject able as web application forms. Depend on specific stored procedure on the database there are different ways to attack.
- Alternate Encodings: In this technique, attackers modify the injection query by using alternate encoding, such as hexadecimal, ASCII, and Unicode. Because by this way they can escape from developer’s filter which scan input queries for special known “bad character”. For example attacker usechar(44) instead of single quote that is a bad character.
- Inference: By this type of attack, intruders change the behaviour of a database or application.There are two well-known attack techniques that are based on inference: blind-injection and timing attacks.
- Blind Injection: Sometimes developers hide the error details which help attackers to compromise the database. So the SQLIA would be more difficult but not impossible. An attacker can still steal data by asking a series of True/False questions through SQL statements.
- Timing Attacks: A timing attack lets an attacker gather information from a database by observing timing delays in the database’s responses. This technique uses an if-then statement for injecting queries. WAITFOR is a keyword along the branches, which causes the database to delay its response by a specified time.
Paper: Sharma, C. and Jain, S.C. (2014) Analysis and classification of SQL injection vulnerabilities and attacks on web applications. In 2014. IEEE. pp. 1–6
Orderwise SQLlA- The order injection attacks are implemented when the code is injected into user’s code (directly or indirectly) to gain unlimited and unauthorized access [11]. We can also categories these order attacks on the basis of deployment in the application/system. These order type attacks are discussed in detail in next section.
Blind SQLlA- There is another type of SQL injection attack called Blind SQL injection attack. It is different om an Orderwise SQL injection attack. In this attack the attacker gets access to the sensitive data by asking a series of true and false questions through SQL statements [14]. The information is extracted based on the answers provided by the application. In this scenario instead of getting the error messages the attacker gets the desired data.
Against Database SQLlA: – The most commonly used attack by attacker to extract data om database server in form of SQL query. In this classi cation attacker mostly uses input validation vulnerabilities to plan the SQL injection attack [10]. The detection and protection om this attack is very dif cult even IDS and rewall does not able to detect these types of attacks because attacks are cra ed om SQL statement which is syntactically co ect for IDS and rewall.
A. FIRST ORDER INJECTION ATTACK
First-order Injection Attacks are basic attacks. The attacker receives the desired result immediately by direct response om the application with which they are interacting. For example – E-mail with an attachment [9] [10].
B. SECOND ORDER INJECTION ATTACK
In second Order Injection Attack the injected malicious code is not activated immediately a er insertion. Infect the attacker waits for subsequently inputs by the user
There are various attacks category in the second order attack [2] [8].
these are split into 4 sub categories
LATERAL INJECION ATTACK
In this category the attacker exploits PLSQL (Structure Query Language) procedure that does not take input from use.
BLIND ATTACKS
as other papers
PAPER: Kindy, D.A. and Pathan, A.-S.K. (2012) A Detailed Survey on Various Aspects of SQL Injection in Web Applications: Vulnerabilities, Innovative Attacks, and Remedies. arXiv.org
Tajpour, A. and Shooshtari, M.J.Z. (2010)Evaluation of SQL Injection Detection and Prevention Techniques. IEEE
There are loads of papers on this:
Kumar, P. and Pateriya, R.K. (2012)A survey on SQL injection attacks, detection and prevention techniques.In2012. IEEE. pp. 1–5
Tautologies: This type of attack represent to the SQL manipulation catego in which attacker can inject malicious code into que , it is based on the conditional statement. For e le a query for login:
SELECT * FROM User WHERE UserName = 'admin' and Password='123456'.
In this query an attacker can inject OR 1=’1′. The resulting query will be:
SELECT * FROM User WHERE UserName=" OR1='1'; -- and Password='123456'.
There are examples and explanations for each type!
Classification of SQLI attacks
what is an sql injection attack
Static Analysis
Sql Injection attack types

Leave a Reply
You must be logged in to post a comment.