What is an sql injection attack? All websites process data entered by users. An input-validation attack is when unexpected user input is processed by a web server or database and an error occurs.
What is an sql injection attack?
“An SQL Injection Attack (SQLIA) occurs when an attacker attempts to change the logic, semantics or syntax of a legitimate SQL statement by inserting new SQL keywords or operators into the statement.” Halfond, W.G.J. and Orso, A. (2005)
An attack surface is, basically, a user input. These take the form of arguments in GET and POST requests, HTML Forms, Cookie values, and Browser environment values. All are attack surfaces for input-validation attacks.
There are lots of different input-validation attacks:
- Buffer Overflows
- Canonicalisation [path over-run]
- Script Attacks – Cross-site Scripting (XSS), Embedded Scripts, Cookies and Predefined Headers
- Boundary checking
- SQL Injection and Datastore Attacks
- Command Execution
SQL injection is one type of input-validation attack.
There are countermeasures to these attacks.
- Server-side input validation
- Character encoding
- Regular expressions
- Strong data-typing
- Proper Error Handling
- Requiring Authentication
- Least Privilege Access
Halfond, W.G., Viegas, J. and Orso, A. (2006) A Classification of SQL Injection Attacks and Countermeasures is an excellent paper on sql injection. This paper has an excellent section on Injection Mechanisms. It shows the way in which SQL code is modified to perform the injection attack – the attack vectors. These are classified as User inputs, Cookies, Server variables and Second order injection. Second order injections are seeding an SQL injection into a database in order for that attack to be triggered later.
A section on attack intent outlines the various reasons for an attacker to want to exploit the database:
- Identifying injectable parameters
- Performing database fingerprinting
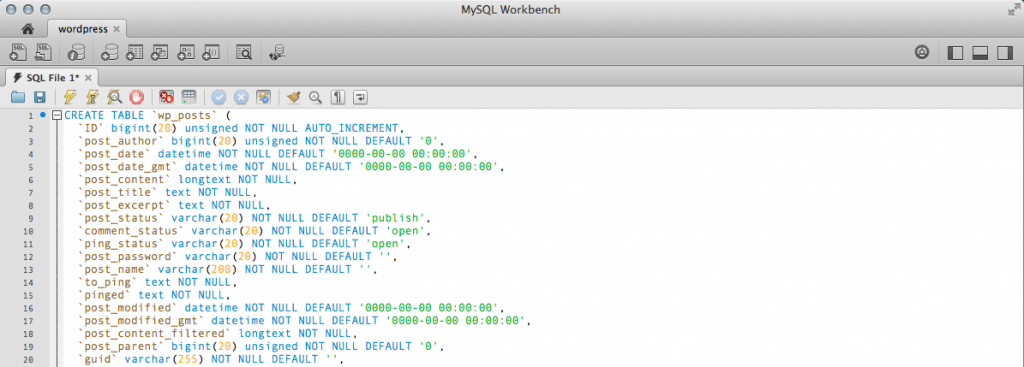
- Determining database schema
- Extracting data
- Adding or modifying data
- Denial of service
- Evading detection
- Bypassing authentication
- Privilege escalation
- Executing remote commands
There is a section on SQLi types, which expands on the Halfond and Orso (2005) AMNESIA paper, adding:
- Tautologies: injecting code into a conditional statement so that it always evaluates as true
- Illegal / locally incorrect queries: essentially generating an error in the database
- Union queries: essentially adding ‘UNION SELECT ‘ to the end of existing queries
- Piggy Back queries: essentially adding a delimiter (;) and a second query to existing queries
- Stored procedures: executing / injecting / modifying stored procedures
- Inference: inferring information, e.g. exploitable parameters, when no usable error reporting is viewable
- Alternate encodings: using alternative character encoding to generate errors
There is an excellent section on detection methodologies:
- Black box testing
- Static code checkers
- Combined static and dynamic analysis
- New query development paradigms
- Intrusion detection
- Proxy filters
- Instruction set randomisation
Hopefully this short post answers the question “what is an sql injection attack?”, and provides you with some other sources to research. You may want to check out a Classification of SQLI attacks and SQL Injection Types

Leave a Reply
You must be logged in to post a comment.