This is a simple Vega scanner tutorial for beginners on XSS scanning with vega scanner in kali linux.
Vega is an open-source web vulnerability scanner designed for finding security issues in web applications. It is particularly favored for its user-friendly graphical interface, making it accessible for both security professionals and those new to vulnerability scanning. Developed in Java, Vega allows users to detect common vulnerabilities such as SQL injection, cross-site scripting (XSS), and other security flaws that may exist within web applications.
Vega Features:
- Graphical User Interface: Vega’s GUI simplifies the process of configuring scans and interpreting results, which is especially beneficial for users who may not be comfortable with command-line tools. This interface makes it easy to navigate through various options and understand scan outcomes.
- Active and Passive Scanning: Vega utilizes both active and passive scanning techniques. Active scanning sends specially crafted requests to the target web application, while passive scanning analyzes the application’s responses to identify potential vulnerabilities without actively probing.
- Extensive Plugin Support: Vega supports a range of plugins, enabling users to extend its functionality. This includes custom scripts for specific tests or additional vulnerability checks, making it adaptable to various testing needs.
- Reporting Capabilities: After scanning, Vega provides detailed reports that outline identified vulnerabilities, their severity levels, and recommended remediation steps. This feature helps developers and security teams prioritize fixes based on risk.
- Community and Documentation: Vega benefits from an active community that contributes to its ongoing development and improvement. Comprehensive documentation and support forums provide users with resources to optimize their use of the tool.
VEGA is an open-source web security scanner, written in java with a GUI. you can scan for XSS issues and can also scan for SQL injection vulnerabilities. In this short introduction tutorial I’ll explain how to do a basic XSS scan for an entire site, but also explain how you can set VEGA to scan a single page. You can find more here
Vega scanner tutorial for beginners
Kali linux already has vega vulnerability scanner installed, so you don’t need to install it. To start VEGA, just go to:
Applications > Kali Linux > Web Applications > Web Vulnerability Scanners > VEGA.
VEGA will launch.
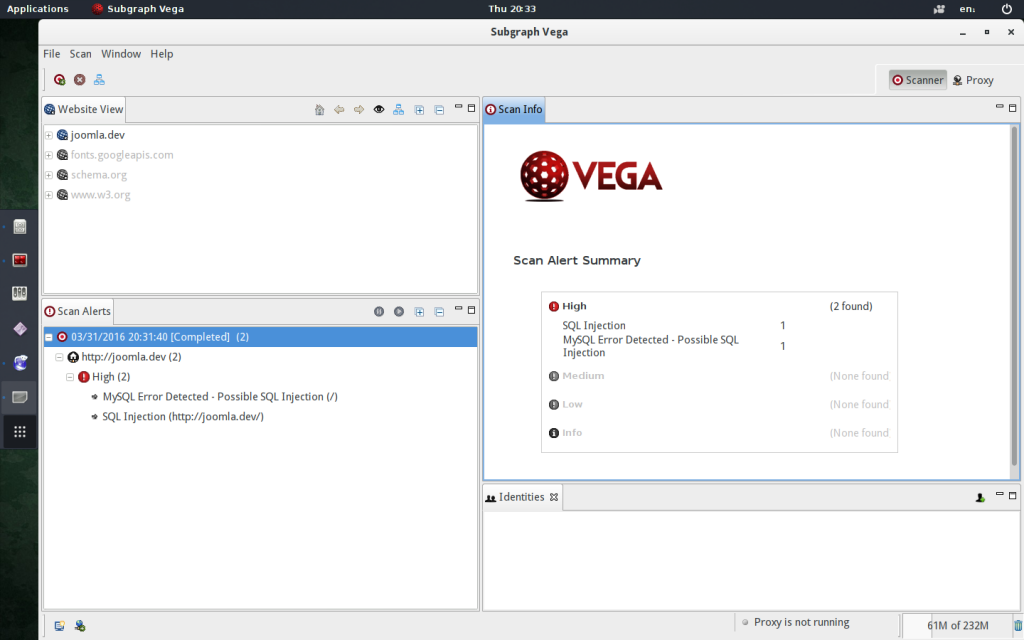
Scanning with VEGA
To start a scan that will crawl the entire site and only check for XSS:
- Click scan > ‘start new scan’ .
- In the dialog that appears, enter your target websites url as the ‘base’
- Click next.
To scan a single page only:
- Click ‘Choose a Target Scope’.
- Then Click ‘Edit Scopes’.
- Next, either add a new scope, or edit an existing one.
- Add each url to the scope.
- Click ‘OK’.
By default vega vulnerability scanner will scan for lots of different vulnerability types.
Header Injections.
Directory Traversal Attacks.
URL Injection Attacks.
XML Injection Attacks.
XSS Injections.
Blind SQL Injections.
Shell Injection Attacks.
Remote file include Attacks.
String Format attacks.
OS Command Injection Attacks.
This is just the first page of the modules section, there are quite a lot to choose from!
XSS Scanning with VEGA scanner
To scan only for XSS you need to:
Unselect all the pre selected options.
(Just click the checkbox next to the expanders for both the categories – injection modules and response processing modules) then:
Under injection modules, Click ‘XSS’.
Click ‘finish’ and wait till the scan completes.
There is excellent documentation available:
Vega wiki
(The section on the vega-proxy is probably what you want to read…)
You might want to also check my metasploit tutorial

Leave a Reply
You must be logged in to post a comment.